Basic RHEL 6 Firewall Configuration
| Previous | Table of Contents | Next |
| Managing RHEL 6 Users and Groups | Configuring RHEL 6 Printers |
<google>BUY_RHEL6</google>
A firewall is a vital component in protecting a computer system, or network of computers from external attack (typically from attack via an internet connection). Any computer connected directly to an internet connection must run a firewall to protect against malicious activity. Similarly, any internal network must have some form of firewall between it and an external internet connection.
In keeping with other Linux distributions, Red Hat Enterprise Linux 6 is supplied with powerful firewall technology known as iptables built-in. Entire books can, and indeed have, been written about configuring iptables. If you would like to learn about iptables we recommend Linux Firewall Configuration - Packet Filtering and iptables which can be found online at:
http://www.linuxtopia.org/Linux_Firewall_iptables/index.html
Fortunately RHEL 6 also provides some tools that make firewall configuration easy for the average user. This chapter will cover the steps necessary to configure an RHEL 6 firewall using those tools.
Configuring a Basic RHEL 6 Firewall
To launch the standard RHEL 6 firewall configuration tool, open the desktop System menu and click on Administration followed by Firewall. Alternatively, the tool can be launched from the command-line as follows:
system-config-firewall
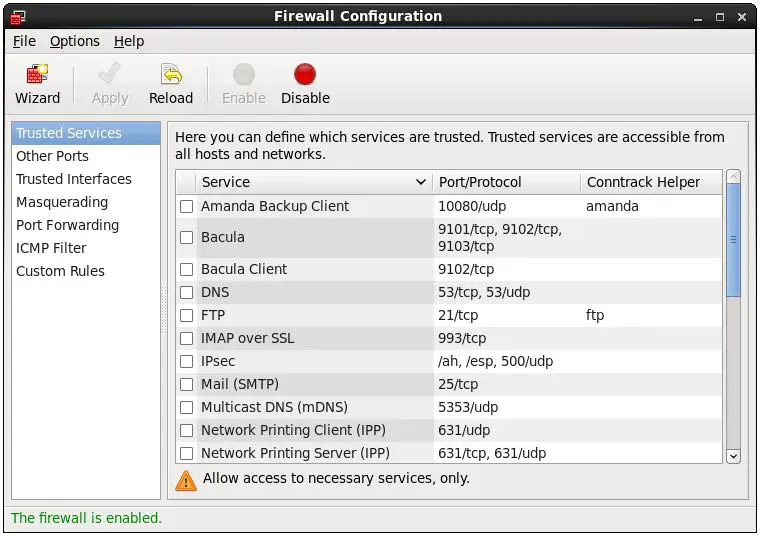
Enter the root password if prompted to do so. Once loaded, the security level tool should appear as follows:
By default, the firewall will be active on a newly installed RHEL 6 system. This is the preferred state for the firewall unless the system is running within a secure network environment or has no network connection. To enable or disable the firewall, click on the corresponding button in the Firewall Configuration window toolbar.
The current status of the firewall is indicated in the status field at the bottom of the window.
Configuring Firewall Settings using the Wizard
By default, the firewall is configured to allow only secure shell (SSH) access to the system and views any network adapters installed as untrusted devices. These settings may be configured manually using the Firewall Configuration tool. Alternatively, the Wizard tool may be used to configure the firewall based on responses to a series of questions. To access the wizard simply click on the Wizard button in the toolbar of the Firewall Configuration tool.
The wizard will ask questions about whether the system is connected to a network, whether you are a beginner or experienced user and, finally, whether the system is being used as a desktop computer or a server. Once the information has been gathered, the wizard will configure the firewall accordingly. For example, if you state that you are a beginner using the system as a desktop computer, the wizard will configure the firewall to allow printing and access to file and printer sharing on other systems using Samba. Beginner mode also disables access to the more advanced firewall configuration options. To change the skill level or configuration profile (desktop or server) use the settings accessible via the Options menu.
Whilst the wizard approach is fine for very basic settings, it will be necessary to manually configure settings for more advanced requirements.
Configuring Firewall Port Settings
The main area of the Firewall Configuration tool consists of a list of categories in the left hand pane and the current corresponding settings for that category in the right hand panel.
The Trusted Services category essentially defines which TCP/IP ports are open to traffic on the firewall. There a number of so called known ports which are assigned to specific servers (such as port 80 for a web server).
A summary of the primary services is as follows:
- SSH - The secure shell provides an encrypted mechanism for allowing password protected remote access to your system. With SSH you can remotely log into to your system, copy files to and from your system and other systems and perform remote execution of programs. If you need remote access to your system you will need to activate this. If you do not need remote access leave this disabled. Note that the ssh server is not installed by default on RHEL 6.
- Telnet - Telnet provides remote terminal access to your system. It does not use encryption and use is strongly discouraged. Leave this disabled and use SSH instead for remote access.
- WWW (HTTP) - If you are hosting a web server on your RHEL 6 system you will need to enable HTTP traffic through the firewall to enable web page requests to reach the http server. If you do not plan to host a web server, leave this disabled. Note that the Apache web server is not installed by default on RHEL 6 unless specifically requested during the installation process.
- Mail (SMTP) - Specifies whether the firewall blocks Simple Mail Transfer Protocol traffic. This is only necessary if you are hosting a mail server on your RHEL 6 system. If you only use a mail client to download email from a POP3 or IMAP server you can safely leave this disabled. Note that the SMTP server is not installed by default on RHEL 6.
- FTP - Controls whether File Transfer Protocol traffic is permitted through the firewall. Unless you plan to set up an ftp server (unlikely for typical users) leave this option disabled. Note that the FTP server is not installed by default on RHEL 6.
- Samba - The Samba service allows files and printers to be shared between Linux and Windows systems. If this traffic is blocked in the firewall, it will not be possible to use Samba on this system.
A more extensive list of services and ports can be found on-line at:
http://www.techotopia.com/index.php/Primary_TCP/IP_Port_Assignments_and_Descriptions
To activate or deactivate an option simply click on the check box next to the service.
Configuring Other Ports
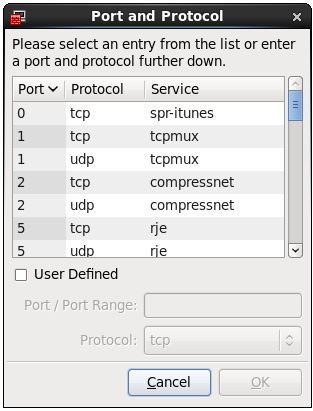
The list of well known ports is not, of course, the only ports available. In fact there are thousands of ports available for use by applications and services. To open a specific port, use the Other ports category of the Firewall Configuration tool. To open a port, click on the Add button to display the Port and Protocol dialog shown below:
This dialog provides a far more extensive list of ports. Either select the desired port from the list, or enter it manually if it is not listed by selecting the User Defined option. When manually defining the port, both the port number and protocol (TCP or UDP) will need to be provided to ensure the firewall does not interfere with traffic on that port.
Configuring Trusted Interfaces
A trusted interface is a network adapter (either physical or software based) on which traffic is known to be coming from a secure network environment. For example, an RHEL 6 system acting as a firewall for an internal network might contain two network adapters, one of which is connected via a gateway or modem to the internet while the other is connected to the secure internal network. In such a situation, the first adapter would be configured as untrusted, since it is exposed to traffic from the outside world. Assuming the internal network is protected by the firewall and other intrusion prevention measures, the second adapter can be considered to be trustworthy.
Masquerading
Masquerading is better known in networking administration circles as Network Address Translation (NAT). When using an RHEL 6 system as a gateway to the internet for a network of computers, masquerading allows all of the internal systems to use the IP address of the RHEL 6 system when communicating over the internet. This has the advantage of hiding the internal IP addresses of any systems from malicious external entities and also avoids the necessity to allocate a public IP address to every computer on the network.
This service is also provided by most routers and gateways so this feature of the RHEL 6 Firewall is rarely used.
Port Forwarding
Port forwarding is used in conjunction with masquerading when the RHEL 6 system is acting as a gateway to the internet for an internal network of computer systems. Port forwarding allows traffic arriving at the firewall via the internet on a specific port to be forwarded to a particular system on the internal network. This is perhaps best described by way of an example.
Suppose that an RHEL 6 system is acting as the firewall for an internal network of computers. One of the systems on the network is configured as a web server. Let’s assume the web server system has an IP address of 192.168.2.20. The domain record for the web site hosted on this system is configured with the public IP address behind which the RHEL 6 firewall system sits. When an HTTP web page request arrives on port 80 the RHEL system acting as the firewall needs to know what to do with it. By configuring port forwarding it is possible to direct all web traffic to the internal system hosting the web server (in this case, IP address 192.168.2.20), either continuing to use port 80 or diverting the traffic to a different port on the destination server. In fact, port forwarding can even be configured to forward the traffic to a different port on the same system as the firewall (a concept known as local forwarding).
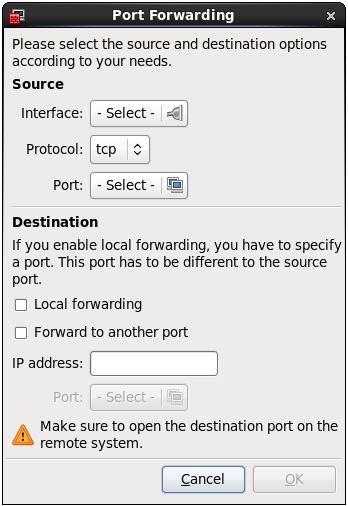
Configure port forwarding by selecting the Port Forwarding category in the Firewall Configuration window and clicking on the Add button. This will display the following dialog:
From within the above dialog, select the network device from which the traffic is to be forwarded (the network device that handles traffic coming from the internet), the protocol and port for which the forwarding is to be effective and the IP address of the system on the internal network to which the traffic is to be diverted. Optionally, also provide an alternate port number on the target system if required.
To forward traffic to a different port on the local system (in other words the system running the firewall), select the Local forwarding option and specify the destination port.
ICMP Filtering
The Internet Control Message Protocol (ICMP) is used by client systems on networks to send error messages to each other. It is also the foundation of the ping command which is used to by network administrators and users to detect whether a particular client is alive on a network. The ICMP Filtering category allows for the blocking of specific ICMP message types. For example, an administrator might choose to block incoming ping (Echo Request) ICMP messages to prevent the possibility of a ping based denial of service (DoS) attack (where a server is maliciously bombarded with so many ping messages that it becomes unable to respond to legitimate requests).
Custom Rules
The Custom Rules category allows individual iptables rules to be specified and loaded into the firewall. This provides a high level of flexibility to perform tasks such as blocking messages from a specific IP address or ranges of addresses. The power and flexibility of iptables allows just about any imaginable restrictions to be placed on the traffic passing through the firewall. This very power, unfortunately, makes a detailed overview of the technology far beyond the scope of this book.
Configuring the Firewall from a Terminal using iptables
In addition to using the graphical tool to configure firewall rules, the iptables command may also be used at the command prompt. To view the current iptables settings, the following command may executed in a terminal window:
iptables -L Chain INPUT (policy ACCEPT) target prot opt source destination Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
As illustrated in the above output, no rules are currently defined. Whilst this may appear to be an unsafe configuration it is important to keep in mind that a newly installed RHEL 6 system also has few services running by default, making the ports essentially useless to a potential attacker. It is not possible, for example, to remotely access a web server simply because the httpd service is installed or running by default. Once services begin to be activated on the system, however, it will be important to begin to establish a firewall strategy by defining iptables rules.
A number of methods are available for defining iptables rules, including the use of command line tools and configuration files. For example, to block access to port 25 (used by the SMTP mail transfer protocol) from IP address 192.168.2.76, the following command could be issued in a terminal window:
iptables -A INPUT -s 192.168.2.76 -p tcp --destination-port 25 -j DROP
If we now check the current rules, we will see that this one is now listed:
iptables -L Chain INPUT (policy ACCEPT) target prot opt source destination DROP tcp -- 192.168.2.76 anywhere tcp dpt:smtp Chain FORWARD (policy ACCEPT) target prot opt source destination Chain OUTPUT (policy ACCEPT) target prot opt source destination
The rule may subsequently be removed as follows:
iptables -D INPUT -s 192.168.2.76 -p tcp --destination-port 25 -j DROP
Given the complexity of iptables it is not surprising that a number of user friendly graphical configuration tools (such as Guarddog and Firestarter) have been created to ease the rule creation process.
<google>BUY_RHEL6_BOTTOM</google>
| Previous | Table of Contents | Next |
| Managing RHEL 6 Users and Groups | Configuring RHEL 6 Printers |